A healthtech founder I was on a call with last month had already spent $40,000 with a dev shop in Eastern Europe. The app worked. The video calls connected. Appointment scheduling ran smoothly. He was three weeks from launch.
Then his first enterprise hospital client sent over their vendor security questionnaire.
The app had no audit logs. PHI was being stored in plaintext in one database table. His analytics tool, a popular third-party product was capturing form inputs that included patient names and diagnosis codes. No Business Associate Agreement existed with anyone except AWS.
He needed 4 more months and another $60,000 to fix it. The hospital client moved on.
I’ve seen this story repeat across 100+ healthcare products the EngineerBabu team has shippe, the ones that succeeded and the ones that didn’t. The single most expensive mistake in healthcare app development is treating HIPAA compliance as a feature you add before launch rather than an architecture decision you make before writing the first line of code.
This guide is what I wish every healthtech founder read before they started. Not the legal version. The builder’s version.
What Is a HIPAA Compliant App?
A HIPAA compliant app is a healthcare application that meets the technical, administrative, and physical safeguard requirements of the Health Insurance Portability and Accountability Act.
It protects Protected Health Information (PHI) through end-to-end encryption (AES-256 at rest and TLS 1.3 in transit), role-based access controls, immutable audit logging, and signed Business Associate Agreements with every third-party vendor that handles patient data.
HIPAA compliance is not a one-time certification. It is a continuous architectural and operational approach that must be integrated from the very beginning of the app development process to ensure patient data security, privacy, and regulatory compliance at every stage.
Does Your App Actually Need HIPAA Compliance?
Before architecting anything, answer this question honestly: does your app create, receive, maintain, or transmit Protected Health Information on behalf of a covered entity?
If yes, you need HIPAA compliance. Full stop.
-
PHI includes more than most founders realize
It’s not just medical records. It’s any information that can identify a patient combined with their health condition, treatment, or payment. That includes names, email addresses, phone numbers, IP addresses, dates of service, and appointment records, when linked to health data.
Here’s what trips up early-stage teams:
A fitness app tracking generic step counts? No HIPAA required. The same app syncing to a clinic’s EHR and sharing data with a physician? Now you’re handling PHI and HIPAA applies.
A mental health app where users journal their symptoms privately? Probably not PHI. The same app where therapists review those journals as part of clinical care? Now you have a covered entity relationship and PHI flows through your product.
-
The 2026 enforcement reality
The HHS Office for Civil Rights updated HIPAA violation penalties in January 2026, they now range from $145 per violation up to $2,190,294, per violation, not per incident. The average healthcare data breach in the USA cost $10.9 million in 2025.
Criminal penalties for intentional misuse of PHI go up to $250,000 and 10 years imprisonment.
When a client asks if their app “needs” HIPAA compliance, the real question is whether they can afford to find out the hard way that it did.
The Foundation: Business Associate Agreements (BAAs)
Here’s the rule that most founders learn late and painfully: if a vendor touches PHI without a signed BAA, you are in violation. Every single time.
A Business Associate Agreement is a legally binding contract required by HIPAA. It establishes that any third-party vendor handling PHI on your behalf: cloud providers, email services, analytics platforms, AI APIs, video infrastructure is contractually responsible for protecting that data.
No BAA means no compliance. Regardless of encryption. Regardless of how reputable the vendor is.
-
The BAA checklist every healthcare team needs
The major cloud providers like AWS, Microsoft Azure, and Google Cloud, all sign HIPAA BAAs and offer HIPAA-eligible services. But here’s the critical nuance: signing a BAA with AWS does not mean every AWS service is covered.
AWS’s BAA covers specific HIPAA-eligible services including EC2, S3, RDS, DynamoDB, Lambda, API Gateway, CloudTrail, and KMS. Services outside that list including some AWS analytics and machine learning products are not covered under the BAA. You are responsible for knowing the difference.
-
The AI API trap that’s catching teams in 2026
This is the mistake I’m seeing most frequently right now. Teams building AI features into healthcare apps are sending PHI to LLM APIs without realizing the BAA requirements.
The standard OpenAI API is not HIPAA compliant. ChatGPT, the web interface and mobile app is not HIPAA compliant for PHI.
However, GPT-4o and other OpenAI models can be used compliantly if accessed through Microsoft Azure OpenAI Service under Microsoft’s HIPAA BAA, or through the OpenAI API with a signed enterprise BAA (request at baa@openai.com, typically approved in 1–2 business days for healthcare organizations).
The same logic applies to Anthropic’s Claude, the standard API requires a separate enterprise BAA for PHI processing. AWS Bedrock and Google Vertex AI provide pathways to compliant access for multiple foundation models under their respective cloud BAAs.
One more trap: no major AI coding tool signs a BAA. Cursor, GitHub Copilot, Replit, Bolt — none of them. If a developer pastes real patient data into these tools during development — which happens more often than compliance teams know, that’s a HIPAA violation. Not a near-miss. A violation.
Practical rule: before any new vendor goes into your architecture, ask one question: “Will you sign a BAA?” If no, they don’t touch PHI. No exceptions.
The 5 Technical Safeguards You Build From Sprint One
HIPAA’s Security Rule defines technical safeguards as the technology and related policies protecting ePHI (electronic Protected Health Information). These are not optional modules. They are foundational infrastructure built before business logic.
-
Encryption: everywhere, always
All PHI must be encrypted at rest using AES-256 and in transit using TLS 1.3. There is no “light” encryption in healthcare. Your database fields containing PHI are encrypted. Your S3 buckets storing patient documents are encrypted. Your API calls transmitting health data use TLS 1.3 with enforced certificate validation.
The practical architecture decision: keep PHI in a separate, dedicated database from your non-PHI application data. This means you only decrypt when genuinely required, which limits exposure surface, improves performance, and creates a clean separation that auditors can verify instantly.
-
Role-Based Access Control (RBAC) enforced at the data layer
HIPAA’s minimum necessary standard requires that each user sees only the PHI their role requires. A receptionist should not see clinical notes. A billing clerk should not see diagnoses. A referring physician should not see a patient’s psychiatric records.
“Doctor sees their patients, admin sees billing” is not RBAC. Real RBAC means:
- Defined roles with documented permissions
- Minimum-necessary access enforced at the database query level, not just the UI
- Access reviews conducted periodically and documented
- Evidence of who had access to which records and when, producible on demand
The most common failure mode: teams implement role checks in the frontend and assume the backend enforces them. It doesn’t. Every API endpoint that returns PHI must enforce authorization independently.
-
Immutable Audit Logs: 6 years, tamper-proof
HIPAA requires mechanisms to record and examine activity in systems containing PHI. Every access to a patient record, every modification, every failed login attempt, every data export, logged with user ID, timestamp, action type, and affected resource identifier.
Two common mistakes: logging nothing at all, or logging too much and including PHI values in error messages. The correct approach is logging the event, who accessed what, when, without logging the PHI content itself.
Audit logs must be retained for a minimum of 6 years, stored in a tamper-proof system (AWS CloudTrail with CloudWatch is the standard approach), and protected from modification by administrators. Production databases should not contain their own audit trails. The audit system must be architecturally independent.
-
Multi-Factor Authentication and Session Management
HIPAA requires unique user identification and emergency access procedures. In practice: every user account must have a unique identifier.
MFA is required for all accounts with PHI access, use app-based authenticators (Google Authenticator, Authy), not SMS which is unencrypted. Session timeouts of 15 minutes of inactivity are standard. Automatic logoff enforced at both the application and infrastructure layer.
-
Breach Detection and Incident Response
You cannot notify patients of a breach you didn’t detect. HIPAA requires breach notification within 60 days of discovery to affected individuals, immediately to HHS if 500+ records are affected, and to media outlets if 500+ residents of a state are affected.
Build detection before you go live: anomalous access pattern alerts (bulk exports, off-hours access from new IP ranges), failed authentication spike detection, unauthorized role escalation alerts.
AWS GuardDuty and CloudTrail Events provide the monitoring layer. Your incident response plan needs to be a documented, tested procedure not a mental note to figure it out if it happens.
The Architecture Decision That Determines Your Entire Compliance Cost
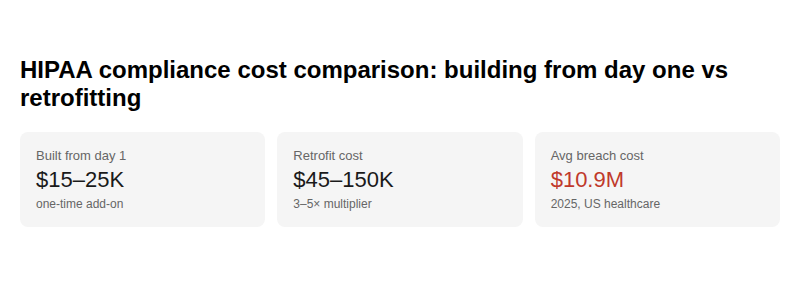
HIPAA compliance built from Day 1 adds approximately $15,000–$25,000 to a standard $60,000–$100,000 healthcare app build.
Retrofitting it after launch costs 3–5× more because you’re not just adding security features. You’re redesigning the data model, developing API or rewriting API authorization logic, migrating unencrypted data with zero downtime, and remediating audit gaps in a live system while real patients are using it.
The “Compliance Creep” pattern kills 68% of healthtech budgets that underestimate it.
Here’s how it works:
You add video consultation. Now you need encrypted video logs with audit trails. You add file uploads for prescriptions. Now you need PHI-classified storage with 30-day deletion policies and access controls. You integrate with an EHR. Now every doctor needs MFA and OAuth 2.0 scoped to minimum necessary data. You add an analytics dashboard. Now every analytics vendor in your stack needs to be audited for PHI exposure and BAAs signed.
Each feature cascades into new compliance requirements. If you didn’t design for it from the start, each cascade is an expensive fix.
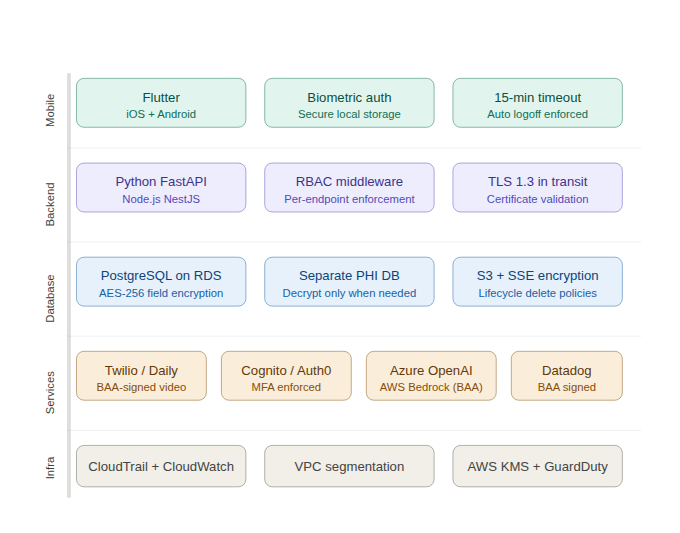
The recommended tech stack for HIPAA-compliant apps in the USA:
| Layer | Recommended Choice | Why |
| Mobile | Flutter (iOS + Android) | Single codebase, biometric auth packages, secure storage libraries |
| Backend | Python FastAPI or Node.js NestJS | HIPAA-aware middleware patterns, strong ecosystem |
| Database | PostgreSQL on AWS RDS | AES-256 encryption, BAA covered, field-level encryption support |
| File Storage | AWS S3 with server-side encryption | HIPAA-eligible, BAA covered, lifecycle policies for deletion |
| Video | Twilio Video or Daily.co | Both offer HIPAA BAAs, WebRTC-based, tested in clinical environments |
| Authentication | AWS Cognito or Auth0 Healthcare | BAA available, MFA enforced, HIPAA-eligible |
| Audit Logging | AWS CloudTrail + CloudWatch | Immutable, HIPAA-eligible, 6-year retention configurable |
| AI/LLM | Azure OpenAI or AWS Bedrock | BAA covered, same models as direct APIs |
| Monitoring | Datadog (with BAA) or AWS CloudWatch | PHI-safe monitoring with signed agreements |
What Most Teams Get Wrong: The 6 Mistakes That Trigger OCR Investigations
From shipping healthcare software across the USA and internationally, the EngineerBabu team has seen and helped fix, the same mistakes at scale.
-
Mistake 1: PHI in push notifications
“Your lab results are ready” is fine. “Your HIV test result is negative” is a HIPAA breach, it sends PHI through Apple’s and Google’s notification infrastructure without a BAA. Push notification content must never contain PHI values. Only generic prompts that bring users into the authenticated app to view their data.
-
Mistake 2: Analytics tools capturing form inputs
Google Analytics, Mixpanel, Segment, and Amplitude all have event tracking that can inadvertently capture form field values if implemented carelessly. A patient intake form that tracks every input for “engagement analytics” is transmitting PHI to a third-party without a BAA.
HHS issued explicit guidance on tracking technologies in healthcare apps in 2023 and has pursued enforcement actions since. Audit every third-party script before it touches a page that handles PHI.
-
Mistake 3: SMS for multi-factor authentication
SMS is unencrypted. HIPAA doesn’t explicitly prohibit it, but HHS has stated that SMS-based 2FA does not meet the standard for PHI-accessing accounts. Use app-based authenticators. For voice-based MFA, use services operating under a HIPAA BAA.
-
Mistake 4: Standard Zoom for telehealth
Zoom’s standard consumer product is not HIPAA compliant. Zoom for Healthcare offers a BAA and is HIPAA-eligible but you must explicitly sign that agreement and use the healthcare-specific product configuration. Teams that notice they “use Zoom” for virtual visits and assume it’s covered because “Zoom has a BAA somewhere” are non-compliant.
-
Mistake 5: No formal risk analysis document
HIPAA requires a formal, written, documented risk analysis before any PHI system goes live. Not a mental checklist. An actual document identifying where PHI exists, what threats it faces, and what controls are in place. This is the first thing an OCR auditor requests. Its absence is itself a compliance violation. The ONC SRA (Security Risk Assessment) tool is the standard framework US teams use.
-
Mistake 6: Developers using Cursor/Copilot with real patient data
In 2026, with AI coding tools everywhere, this is the most underappreciated compliance gap in healthcare development. No major AI coding assistant, Cursor, GitHub Copilot, Replit, Bolt, Lovable signs a BAA. Using real patient data in prompts, even for “testing,” is a violation. Development environments must use synthetic data only. Production PHI never touches tools without signed BAAs.
How Much Does It Cost to Build a HIPAA Compliant App in the USA?
This is the question I get on almost every scoping call for a healthcare product. The honest answer has three parts.
- Adding HIPAA compliance to a new build from Day 1 costs $15,000–$25,000 on top of the base development cost. This covers encryption architecture, BAA management, audit logging infrastructure, RBAC design, MFA implementation, security testing, penetration testing, and compliance documentation.
- Retrofitting an existing non-compliant app costs 3–5× more than building it in. The full range is typically $45,000–$150,000+ depending on how deeply non-compliance is embedded in the architecture.
- Ongoing annual compliance maintenance runs $10,000–$30,000 per year: annual risk assessments, security audits, penetration testing, BAA renewals, staff training documentation, and responding to the evolving regulatory landscape. The proposed 2026 HIPAA Security Rule update will require updates to audit control specifications and AI governance documentation for any app using LLMs with PHI.
The framing that helps founders make this decision clearly: the average US healthcare data breach cost $10.9 million in 2025. The probability-weighted cost of a breach far exceeds the cost of building correctly. Compliance is not overhead. It is risk management.
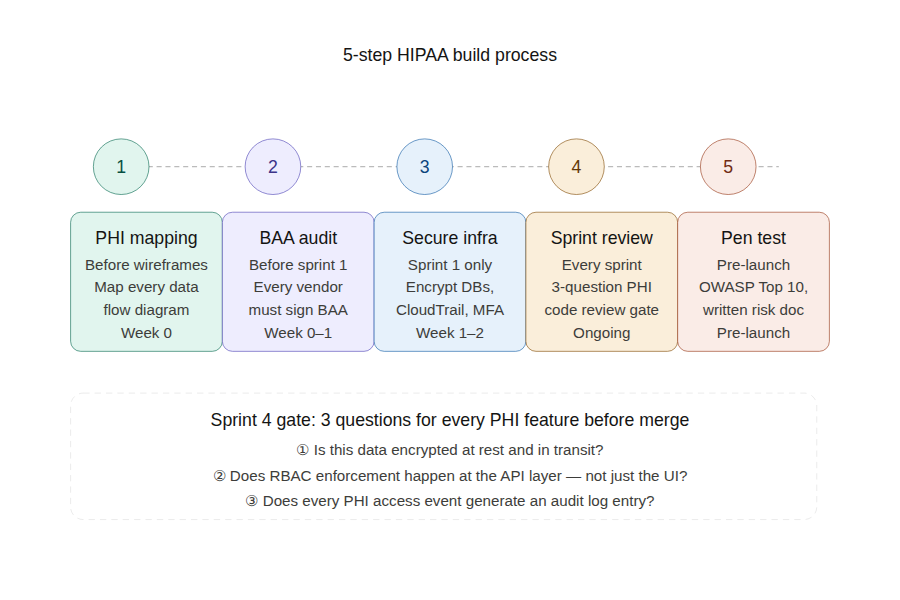
The 5-Step Build Process for HIPAA Compliance
When the EngineerBabu team scopes a healthcare product, this is how we structure compliance from week one.
Step 1: PHI Data Flow Mapping (Before Architecture)
Before any wireframes or architecture diagrams, map every piece of PHI your app will touch. Where is it collected? Where is it stored? Who can access it? How is it transmitted? When is it deleted? Build a data flow diagram. This document becomes the foundation of your risk analysis and tells you exactly where compliance controls need to be applied.
Step 2: BAA Audit of Every Vendor (Before Sprint 1)
List every third-party service in your planned architecture. For each one: Will they sign a BAA? If no, they don’t touch PHI. Replace them before a single line of code is written. This is not a legal exercise. It is an architecture exercise. Vendors without BAAs fundamentally cannot be part of a HIPAA-compliant data path.
Step 3: Security-First Infrastructure Setup (Sprint 1)
Configure your HIPAA-eligible cloud infrastructure, encrypted databases, encrypted S3 buckets, CloudTrail audit logging, Cognito with MFA, VPC network segmentation before any application code is written. The infrastructure is the foundation. Building business logic on top of an unsecured infrastructure means you’re building compliance debt with every feature.
Step 4: Build Compliance Into Every Sprint (Ongoing)
Every feature that touches PHI gets reviewed against three questions before merge: Is this data encrypted at rest and in transit? Does RBAC enforcement happen at the API layer, not just the UI? Does every PHI access event generate an audit log entry? This is a code review discipline, not a launch-week checklist.
Step 5: Penetration Testing and Risk Assessment Before Launch
Professional penetration testing focused on OWASP Top 10 vulnerabilities and healthcare-specific attack surfaces (PHI exposure in APIs, broken object level authorization, insecure direct object references). The written risk analysis document produced from this test is what you send to hospital clients when they ask for your security posture.
The Bottom Line
Building a HIPAA compliant app in the USA is an architecture decision, not a launch checklist.
Every team I’ve seen get this right made the same choices: they mapped PHI flows before writing code, signed BAAs before onboarding vendors, built encryption and audit logging in Sprint 1, and treated compliance as foundational infrastructure rather than a feature set.
Every team I’ve seen struggle made the opposite choices usually with the same justification: “we’ll clean it up before launch.” You won’t. The cascade effect makes it 3–5× more expensive every month you wait.
The EngineerBabu team has shipped healthcare products for clients including Apollo Hospitals, ResMed/Somnoware, and dozens of US-based digital health startups, across telemedicine, remote patient monitoring, AI clinical documentation, and RCM platforms. Every one of them started with this same framework.
If you’re evaluating a healthcare app build and want to talk through the architecture decisions and compliance posture before committing to a vendor or a scope, I’m usually the one on those calls. Reach me directly at mayank@engineerbabu.com.
Author: Mayank Pratap Co-Founder, EngineerBabu Google AI Accelerator 2024 · CMMI Level 5 · 500+ Products · 20+ Countries LinkedIn
FAQ
-
Does my health app definitely need HIPAA compliance?
If your app creates, receives, maintains, or transmits Protected Health Information on behalf of a covered entity, a hospital, clinic, insurance company, or healthcare clearinghouse, yes. The determining factor is not your app’s category but whether PHI flows through it in connection with a covered entity’s operations. When in doubt, consult a healthcare attorney. The cost of that consultation is orders of magnitude less than the cost of a violation.
-
What is a Business Associate Agreement and do I need one?
A BAA is a legally binding contract required by HIPAA before any third-party vendor can handle PHI on your behalf. You need BAAs with your cloud provider, video infrastructure, email service, analytics platform, AI API provider, and any other service that touches patient data. If a vendor won’t sign a BAA, they cannot be part of your HIPAA-compliant architecture, regardless of how reputable or widely used they are.
-
Can I use ChatGPT or OpenAI API for my healthcare app?
ChatGPT’s web interface and mobile app are not HIPAA compliant for PHI. The OpenAI API can be used compliantly with a signed enterprise BAA (request at baa@openai.com) configured for zero data retention. Alternatively, access GPT-4o through Microsoft Azure OpenAI Service under Azure’s HIPAA BAA. The model is identical, the deployment environment and legal agreement determine compliance, not the AI model itself.
-
How much does it cost to build HIPAA compliance into an app from scratch?
Building HIPAA compliance into a new healthcare app from Day 1 adds $15,000–$25,000 to the base development cost. Annual ongoing compliance maintenance, risk assessments, penetration testing, BAA renewals, staff training, runs $10,000–$30,000 per year. Retrofitting compliance into a non-compliant app costs 3–5× more than building it in from the start.
-
How long do HIPAA compliance records need to be kept?
A minimum of 6 years from the date of creation or the date when last in effect, whichever is later. This applies to compliance policies, BAAs, risk analyses, audit logs, and breach documentation. Audit logs specifically must be stored in a tamper-proof system protected from administrator modification.
-
What’s the first thing an OCR auditor checks?
Your written risk analysis. HIPAA requires a formal, documented risk analysis before any PHI system goes live and it must be updated when significant architectural changes occur. Its absence is itself a violation. If your app has evolved since your initial risk analysis but the document hasn’t been updated, you’re non-compliant regardless of the technical controls in place.
-
Can I use Cursor or GitHub Copilot to build my healthcare app?
Yes, for generating code but with strict rules. Never input real patient data into any AI coding tool. None of them (Cursor, Copilot, Replit, Bolt) sign BAAs. Use synthetic data only in development environments. Production PHI must never touch tools operating outside a signed BAA. AI tools accelerate healthcare development by 20–40% when used correctly in a compliant workflow.
-
When should I bring in a HIPAA compliance specialist?
Before architecture decisions are made not before launch. The earlier a compliance specialist reviews your data model, vendor selection, and infrastructure design, the cheaper their recommendations are to implement. A pre-architecture review typically costs $5,000–$15,000. Discovering the same issues during a hospital client’s vendor security evaluation typically costs 10× that and the client relationship.



![How to Build a Telemedicine App in 2026 [Complete Guide] | EngineerBabu 7 How to Build a Telemedicine App in 2026 [Complete Guide] | EngineerBabu](https://engineerbabu.com/blog/wp-content/uploads/2026/06/ChatGPT-Image-Jun-1-2026-03_27_28-PM.png)